VestaCP is having a zero-day bug, which has never been seen before and is very dangerous, causing the server to suffer automatic attacks. If you are using VestaCP, please update immediately.

Information about this bug appeared on 07/04 at VestaCP forum and many other technology forums and attracted many people interested because of its danger level. In addition, many vendors had to shut down a series of VPS attacked by this security flaw.
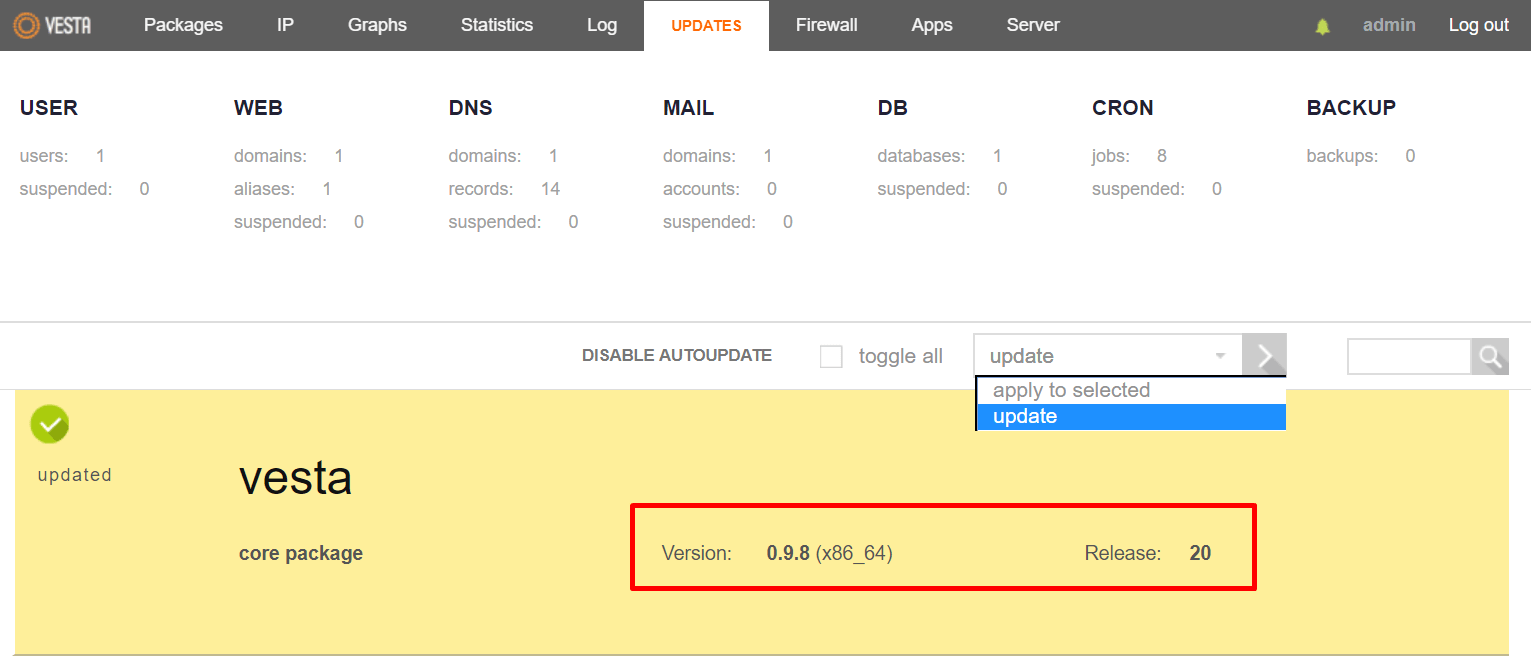
Today, VestaCP released the latest update – 0.9.8-20 – patched and enhanced security.
If you are using VestaCP, immediately update the manager to the latest version in one of two ways:
– Option 1: Accessing VestaCP administration on the website, Updates and core updates
– Method 2: Through SSH# v-update-sys-vesta-all
Review
#v-list-sys-vesta-updates PKG VER REL ARCH UPDT DATE --- --- --- ---- ---- ---- vesta 0.9.8 20 x86_64 yes 2018-04-09 vesta-php 0.9.8 19 x86_64 yes 2018-04-09 vesta-nginx 0.9.8 19 x86_64 yes 2018-04-09 vesta-ioncube 0.9.8 19 x86_64 yes 2018-04-09 vesta-softaculous 0.9.8 19 x86_64 yes 2018-04-09
Note: If you have disabled the previous VestaCP management service then you need to enable it again and run the update:
# systemctl enable vesta && systemctl start vesta
Good luck to you protection of your system!








![[How To] Best Dedicated Server: Choose The Best Dedicated Server For Less](https://easypromocode.com/wp-content/uploads/2020/05/dedicated_server-2-100x65.jpg)

